A former employee leaves on Friday. By Monday, one of your customers mentions that a competitor suddenly knows your pricing, renewal dates, and buying patterns. You check sent emails, cloud access logs, and shared folders, and the problem gets worse fast. Someone appears to have taken information your business spent years building.
That’s the moment business owners start asking what happens if you break a confidentiality agreement. The short answer is simple. It can trigger a lawsuit, an emergency court order, a claim for damages, fee exposure, and a hard-to-repair hit to reputation. In the right case, it can also spill into trade secret claims and regulatory problems.
For a Connecticut business owner, the issue isn’t abstract contract theory. It’s whether you can stop the disclosure quickly, contain the damage, preserve customer relationships, and put yourself in the strongest position if the dispute lands in court or arbitration. If you’re the person accused of the breach, the goal shifts. You need to stop making the situation worse, protect evidence, and assess whether the disclosure was prohibited or whether a defense applies.
The High Stakes of Silence An Introduction to NDAs
A confidentiality agreement, often called an NDA, is a contract that limits who can use or disclose protected information. Businesses use them with employees, contractors, consultants, vendors, investors, and prospective buyers. The point is straightforward. If someone gets access to sensitive information because of a business relationship, the NDA sets the rules for what they can and can’t do with it.
The protected information can take many forms. Sometimes it’s a client list, pricing model, source code repository, manufacturing process, investor deck, customer pipeline, or acquisition plan. Sometimes it’s less dramatic but just as valuable, like margin data, supplier terms, internal forecasts, or strategic rollout timelines. If disclosure gives someone else an unfair shortcut into your business, it’s the kind of information an NDA is designed to protect.
If you want a more basic primer on the contract itself, this overview of what a confidentiality agreement is is a useful starting point.
What an NDA actually does
An NDA doesn’t create secrecy by magic. It does three practical things:
- Defines the protected category so people know what counts as confidential.
- Restricts use and disclosure so the recipient can’t pass the information to outsiders or use it for their own benefit.
- Creates remedies if the relationship breaks down and someone leaks or misuses the material.
Practical rule: If the agreement is vague about what’s protected, enforcement gets harder. If it’s precise, your leverage improves.
Why business owners rely on them
Most companies don’t lose value because someone stole a single document. They lose value because a person who had inside access knew which information mattered and where to use it. NDAs are one part deterrent and one part litigation tool. They tell the recipient the information has legal protection, and they give the injured business something concrete to enforce when trust fails.
That’s why these agreements show up at every stage of growth. Early-stage companies use them before partnership talks. Established companies use them in hiring and vendor relationships. Sellers use them in due diligence. Lenders and financial professionals use them when reviewing internal books, deal structures, or customer data.
Stopping the Leak The Power of Injunctive Relief

When confidential information starts moving, the first priority usually isn’t money. It’s stopping the spread. In litigation, that tool is injunctive relief. Think of it as the emergency brake for a business dispute.
An injunction is a court order telling the other side to stop using, sharing, copying, or distributing the information. Depending on the facts, a company may seek a temporary restraining order first, followed by a preliminary injunction while the case proceeds. In practical terms, that can mean freezing use of a client list, prohibiting contact with certain customers using stolen data, ordering return of files, or blocking further disclosure to a competitor.
Why speed matters
Confidential information loses value when it keeps circulating. Once a trade secret or customer strategy reaches enough people, the damage becomes harder to reverse. That’s why the early phase of an NDA case often moves quickly.
Courts generally focus on whether the moving party can show serious harm that money alone won’t fix. Lawyers and judges often call that irreparable harm. In the NDA context, that usually means a risk that confidential information will keep spreading, customer relationships will be disrupted, or a competitive advantage will be lost in a way that can’t be neatly priced later.
According to this discussion of breach of confidentiality consequences, injunctions have a success rate exceeding 70% when “irreparable harm” is pre-defined, which is one reason careful drafting matters so much on the front end.
What helps and what hurts in court
A business seeking an injunction usually benefits from moving with discipline. That means:
- Preserving proof early. Access logs, download histories, forwarded emails, device records, and witness statements matter.
- Showing actual confidentiality practices. Password restrictions, limited access, file labeling, and offboarding controls help show the information was treated as secret.
- Connecting the breach to a real business risk. Judges respond to concrete harm, not broad outrage.
What hurts is delay. If a company waits too long after learning of the disclosure, the other side will argue the situation wasn’t really urgent. Sloppy internal handling can also weaken the request. If everyone in the company had broad access and the information was never meaningfully protected, the court may question how confidential it really was.
The strongest injunction requests usually come from businesses that can show both contract language and disciplined internal practices.
What an injunction can and can’t do
An injunction can stop further misuse. It can compel return or deletion of material. It can restrict contact with data derived from the breach. What it usually can’t do is rewind every consequence. If a competitor already learned your pricing strategy, the court can control future conduct, but it can’t erase what was seen.
That’s why the first legal question after a breach is often narrow and urgent. How do we stop the leak today?
The Financial Reckoning Monetary Damages for a Breach
Once the immediate leak is addressed, the dispute usually turns to money. That’s where many business owners underestimate the exposure. A breach of an NDA isn’t just about whether someone did something wrong. It’s about what that misconduct cost, what it will cost to contain, and what the contract says happens next.
Courts typically look at damages through a few different lenses. Some are tied to actual loss. Some come from the contract itself. Some involve legal fees that can change the economics of the case dramatically.
Compensatory damages
Compensatory damages are meant to reimburse the injured party for actual harm. In NDA cases, that often means lost profits, damage to the value of proprietary information, or money spent responding to the breach.
A common example is a leaked client list. If a former employee hands that list to a competitor and customers move, the injured business may claim the revenue it would have earned absent the breach. In other cases, the loss is tied to diminished value of internal know-how or to the cost of containment, such as re-securing systems, revising access controls, and investigating the scope of disclosure.
The same source cited above notes that courts award compensatory damages using measures such as lost profits or diminished IP value, and that breaching parties often face prevailing party fee exposure averaging over $100,000 in mid-sized disputes, which can amplify overall financial exposure by 2-3x in the right case.
Liquidated damages
Some NDAs include a liquidated damages clause. That provision tries to set the financial consequence in advance, rather than forcing the injured party to prove every dollar after the breach.
That can be useful when the harm is real but hard to measure. A company may know confidential strategy was disclosed, yet proving the exact economic impact can take months of accounting work and expert testimony. A well-drafted liquidated damages clause can shorten that fight.
Courts don’t automatically enforce every such clause. If the number looks punitive rather than like a reasonable estimate of anticipated harm, it may be challenged. But when drafted carefully, it can quickly alter the settlement dynamic.
Legal fees can become the real pressure point
Many business owners focus on damages and ignore fee shifting. That’s a mistake. In practice, attorney’s fees often become one of the strongest incentives to settle or comply early.
If the NDA includes a prevailing party provision, the loser may end up paying not only its own legal bills but also the other side’s. In a business dispute that moves into injunction practice, document discovery, expert review, and motion work, that risk gets expensive fast.
Here is a practical breakdown:
| Type of Damage | Purpose | Example |
|---|---|---|
| Compensatory damages | Reimburse actual business loss | Lost profits tied to a leaked client list or the cost of mitigating misuse of confidential information |
| Liquidated damages | Apply a pre-agreed financial consequence | Contract sets a specified recovery amount if protected information is disclosed |
| Attorney’s fees and costs | Shift litigation expense to the losing side when the contract allows it | Prevailing party seeks recovery of substantial fees incurred enforcing the NDA |
If the agreement has a fee-shifting clause, the case value is rarely limited to the amount of the original loss.
What damages claims often miss
Some businesses overreach. They describe every business setback after the breach as if the NDA violation caused it. Courts usually want a tighter connection than that. You need a coherent damages theory, documents to support it, and a timeline that makes sense.
The breaching side has its own risks. A weak defense can turn a manageable dispute into a much larger one if the other side can show misuse continued after notice. Continued use after a cease-and-desist letter or after suit is filed tends to make the case worse, not better.
Punitive-style arguments can appear where conduct is especially bad, but the core financial fight in most NDA cases remains compensatory damages, contractual remedies, and fees. In business terms, that means the breach can become costly even before trial.
Drafting for Enforcement How a Strong NDA Enables Remedies
The best NDA litigation usually starts long before the dispute. It starts at drafting. Business owners often sign confidentiality agreements pulled from an old file, a template library, or a prior deal without asking the right question. If this gets breached, will the contract help me enforce my rights?
A strong NDA doesn’t just say “keep this confidential.” It gives a court a workable roadmap. The more clearly the agreement identifies the protected information, the restricted conduct, and the remedy structure, the stronger the enforcement position.
Clauses that matter in the real world
The first clause that matters is the definition of Confidential Information. If that definition is too broad, the other side may argue the contract tried to cover everything and therefore protected nothing with enough clarity. If it’s too narrow, key information may fall outside the agreement.
The second issue is scope. The agreement should explain who may receive the information, for what purpose, and what happens when the relationship ends. Return or destruction obligations matter. So do restrictions on copying, retaining, and using the information for any purpose other than the defined business relationship.
For employers, this guide to non-disclosure agreements for employees highlights why employment-based confidentiality terms need to be specific to the role and the information accessed.
Draft for the remedy you may need
A lot of contracts fail because they mention confidentiality in broad language but say almost nothing about enforcement. That’s shortsighted.
If you expect to seek an injunction in a fast-moving dispute, the contract should say a breach causes irreparable harm and that injunctive relief is appropriate. That won’t win the motion by itself, but it helps frame the issue from the start. If damages are likely to be hard to quantify, a carefully reasoned liquidated damages clause may also improve your position.
A practical NDA often includes:
- A precise confidentiality definition tied to actual business categories.
- Use restrictions that prohibit competitive or personal use, not just public disclosure.
- Return and deletion obligations for files, devices, and cloud-stored materials.
- Fee-shifting language that changes the economics of enforcement.
- Forum and governing law provisions so everyone knows where the fight belongs.
A vague NDA is often worse than no NDA. It creates false confidence, then collapses when you need it most.
What doesn’t work
Overreaching language is a common drafting problem. If the agreement tries to label every routine fact as permanently confidential, enforceability gets harder. So does relying on inconsistent internal practice. A contract may call information confidential, but if the company spreads it casually, stores it without controls, or never limits access, the paper promise starts to look disconnected from reality.
The strongest agreements match the business. They identify what matters, define how it is protected, and anticipate how a court will evaluate the dispute later.
Defenses and Exceptions When a Breach May Be Justified
Many NDA discussions make it sound like any disclosure automatically leads to liability. That’s not accurate. Some disclosures are defensible. Others are required. And in a small but important category of cases, the person accused of breaching the agreement may have had a legal right, or even a legal obligation, to speak.
That doesn’t mean “I thought it was okay” is a defense. It means the context matters.
When disclosure may not be a breach
Several recurring defenses appear in confidentiality disputes:
- The information was already public. If the material was lawfully available through public sources, the NDA may not cover it.
- The information was independently developed. A party who created or obtained the same knowledge without using confidential material may challenge the claim.
- The disclosure was compelled. Court orders, subpoenas, and certain formal investigations can override private confidentiality obligations, though the recipient usually still needs to handle the disclosure carefully.
- The contract is unenforceable as written. Overbroad definitions, unreasonable duration, or poor drafting can matter.
None of those defenses should be assumed. They are fact-dependent, and timing matters. For example, a person responding to a subpoena should usually preserve the documents, review the NDA, and seek advice before producing material. “Compelled disclosure” is not a free pass for broad voluntary sharing.
Whistleblower and regulatory exceptions
The most important modern exception for some professionals involves whistleblower and regulatory reporting. NDAs generally cannot be used to shield unlawful conduct from regulators.
That issue matters sharply in securities and financial services disputes. According to this discussion of NDA breach exceptions and escalation risk, a Q1 2026 FINRA report noted a 40% rise in successful whistleblower NDA challenges in securities arbitration, allowing advisors to report misconduct without penalty when the filing is handled properly. The same source states that 15% of federal indictments involved a prior NDA in 2025 cases where trade secret theft overlapped with criminal exposure under the Defend Trade Secrets Act.
That combination matters. Some disclosures are protected because they serve a regulatory or public interest function. Other disclosures become more dangerous when they look less like whistleblowing and more like misappropriation.
Financial advisors and firms should treat Form U5 disputes, internal complaints, and regulator-facing disclosures as a separate legal category, not as ordinary NDA fights.
The line between protected reporting and risky disclosure
A valid whistleblower disclosure is not the same thing as venting to a competitor, posting documents online, or sending internal files to people who have no role in the complaint. The safest path is targeted disclosure through the proper channel.
For Connecticut business owners, that means the right response depends on which side you’re on. If you believe an employee used an NDA exception as cover for theft, investigate methodically. If you’re the employee or advisor considering disclosure to a regulator, act with counsel before sending anything.
Criminal exposure isn’t automatic, but it isn’t imaginary either
Most NDA cases remain civil disputes. They are fought over injunctions, damages, and contract rights. But when the facts involve trade secret theft, competitive misuse, or evidence of intentional taking, the case can move beyond ordinary contract law.
That’s especially true when someone copied information, kept using it after separation, or transferred it for competitive gain. The point for business owners is practical. Don’t assume “it’s just an NDA case.” Sometimes it is. Sometimes it becomes more serious.
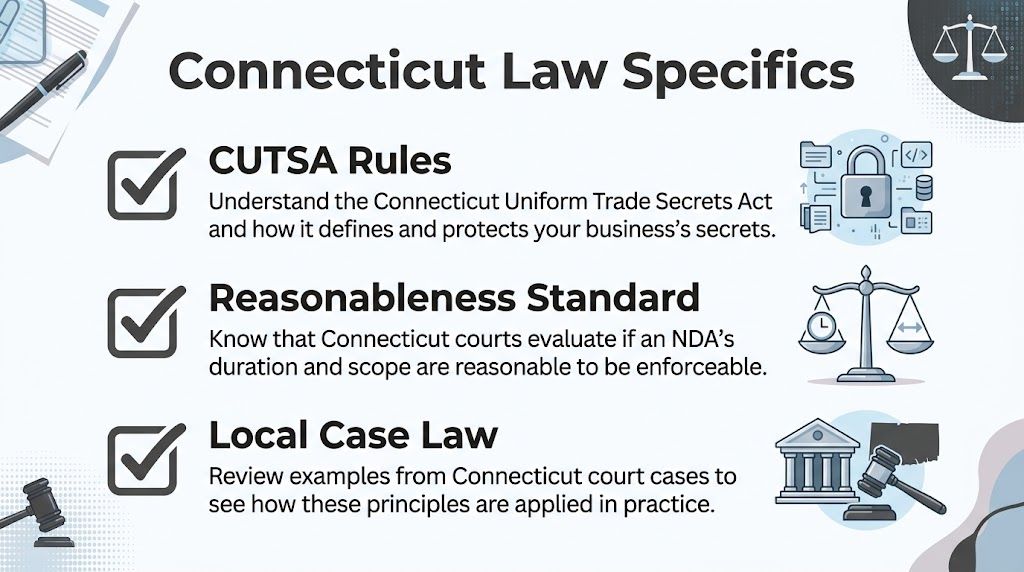
Connecticut Law Specifics for Local Businesses
Connecticut businesses shouldn’t analyze confidentiality disputes as if they exist only in a generic national framework. State law, local procedure, and how Connecticut judges evaluate reasonableness all shape the risk.
In many cases, a breach of a confidentiality agreement sits next to a trade secret claim. If the information qualifies as a trade secret, the contract claim may be only part of the dispute. The business may also pursue statutory remedies under Connecticut law. If it doesn’t qualify as a trade secret, the NDA still may matter, but your proof burden changes.
How Connecticut businesses should think about protection
A Connecticut court will usually care about more than the words on the page. It will look at whether the company treated the information as confidential. That means limiting access, controlling copies, using secure systems, documenting offboarding, and keeping business-sensitive material out of casual circulation.
Many businesses weaken their own cases. They draft a decent agreement, then undermine it operationally. Files sit in shared drives with broad access. Sensitive topics get discussed in hallways, restaurants, and conferences. Departing employees keep access longer than they should.
That last point isn’t hypothetical. A clinical observation study on confidentiality breaches in professional settings documented one breach every 62.5 hours, found that 51.4% were caused by physicians, and that 37.9% occurred in public areas such as corridors and elevators. The setting was healthcare, but the lesson applies far beyond hospitals. Informal disclosure is a business risk in every professional environment.
CUTSA and practical overlap with NDA claims
For Connecticut companies, the Connecticut Uniform Trade Secrets Act often becomes part of the conversation when the leaked material has independent economic value because it isn’t generally known and the owner took reasonable steps to protect it.
That overlap matters because businesses sometimes think an NDA alone solves everything. It doesn’t. The contract is one tool. Trade secret law may provide another, but only if the facts support it. If you want a practical overview of those protections, this resource on how to protect trade secrets is worth reviewing.
What local businesses should tighten now
Before a dispute arises, Connecticut businesses should review three areas:
- Access discipline. Sensitive material should be limited by role, not shared by convenience.
- Offboarding controls. Cut off access promptly, collect devices, and confirm return or deletion obligations in writing.
- Public-setting habits. Train employees not to discuss customer, deal, or pricing details in elevators, corridors, restaurants, or common areas.
Confidentiality failures often come from routine behavior, not dramatic theft. Loose conversation and weak access control create litigation exhibits.
A business that combines reasonable contract language with visible internal controls stands in a much stronger position if a dispute reaches a Connecticut court.
A Breach Occurred What Are the Immediate Next Steps
When a confidentiality breach happens, businesses lose time by arguing about blame before they lock down facts. The first day matters. The first week matters more. If regulated data is involved, delay can create separate legal problems beyond the contract dispute itself.
That’s clear in healthcare. As explained in this overview of healthcare data breach consequences and reporting duties, telehealth company Cerebral faced a $7.1 million settlement for impermissible data disclosure, affected individuals generally must be notified within 60 days, and breaches affecting more than 500 individuals can trigger media notification requirements. Most Connecticut businesses aren’t HIPAA-regulated entities, but the lesson carries over. A structured response limits downstream damage.
If your business suffered the breach
Start with evidence, not accusation.
- Preserve records immediately. Save emails, chat logs, access logs, device records, cloud activity, and screenshots. Don’t let routine deletion policies wipe out evidence.
- Contain access. Suspend accounts, rotate credentials where appropriate, and restrict any shared folders tied to the incident.
- Map the information involved. Identify exactly what was disclosed, who had access, who received it, and whether the material is customer data, financial data, trade secret material, or regulated information.
- Send a targeted legal notice. A cease-and-desist letter can demand return, deletion, and non-use, but it needs to fit the facts. If you’ve received one, this guide on how to respond to a demand letter gives a practical overview of the issues.
- Coordinate legal and technical response. If systems or customer data are involved, a technical incident team may be as important as litigation counsel. Businesses looking for an operational framework can review this Data Breach Incident Response resource for containment and response planning.
If you’re accused of the breach
Panic creates bad evidence. Stop and narrow the problem.
- Stop any further use or disclosure. Don’t forward, copy, or “clean up” files.
- Preserve your communications and devices. Deleting messages after notice often makes the case worse.
- Identify what you received and did. There is a major difference between accidental receipt, negligent handling, and intentional use.
- Review the contract and context. The NDA’s wording matters. So does whether the information was confidential, public, independently known, or shared under legal compulsion.
- Get legal advice before replying in detail. Quick admissions in email can box you into a position that isn’t legally accurate.
A practical response checklist
Here’s the shortest usable version for both sides:
- Secure the information
- Preserve the evidence
- Assess legal duties
- Control communications
- Decide quickly whether injunctive relief or negotiated resolution makes more sense
Early mistakes are expensive. Casual emails, incomplete investigations, and delayed preservation can reshape the entire case.
In some disputes, the right move is immediate litigation. In others, a tightly negotiated standstill, return protocol, and certification process can contain the issue without a public fight. The facts decide that.
Protecting Your Business and Your Future
Breaking a confidentiality agreement can lead to injunctions, damages claims, fee exposure, and reputational fallout. For the business that suffers the breach, the key is speed, proof, and a contract built for enforcement. For the person or company accused of the breach, the key is to stop the conduct, preserve evidence, and determine whether a real defense or exception applies before making the situation worse.
If your business handles sensitive data across borders or works with overseas partners, a practical outside resource is this UK Business Playbook for Data Breach Response, which offers a useful operational perspective on incident response planning.
If you want to discuss your business law matter, contact Kons Law at (860) 920-5181.