Before you can protect your company’s most valuable secrets, you have to know what they are. This isn't just a casual list-making exercise; it's a deep dive into your operations to pinpoint the exact confidential information that gives you an edge over the competition. This could be anything from your client lists and secret formulas to those unique internal processes that make your business tick.
Identifying Your Most Valuable Hidden Assets
Many business owners I talk to think trade secrets are reserved for tech giants or companies with a portfolio of patents. The reality is, your most valuable assets are often hiding in plain sight, woven into the fabric of your daily work. The first real step to protecting them isn't drafting a legal document—it's conducting a thorough internal audit to create a detailed inventory.

The goal here is simple: understand precisely what information gives you a competitive advantage and why it's so important. Both Connecticut law and the federal Defend Trade Secrets Act (DTSA) offer powerful protections, but they don't apply automatically. Your information only qualifies if it has independent economic value because it's not widely known and you’ve made reasonable efforts to keep it secret.
Beyond the Obvious: What Qualifies as a Trade Secret?
You have to think bigger than just secret recipes and complex algorithms. A surprising amount of business information can be legally classified as a trade secret, provided it meets the standard. A good rule of thumb is to look at different parts of your business and ask a simple question: "Would a competitor pay good money to know this?"
Consider some of these common, yet often overlooked, categories:
- Customer and Supplier Intel: We're not talking about a simple list of names from a public directory. A curated customer list with detailed purchasing histories, contact preferences, and specially negotiated pricing is a classic trade secret. The same goes for supplier lists that include special terms, pricing, or key contacts you've cultivated over years.
- Internal Processes and Methods: This is the "how we do it" magic. It could be a unique manufacturing technique that slashes waste, a proprietary software script you developed for data analysis, or a specific workflow for managing logistics that competitors haven’t figured out.
- Financial and Strategic Data: Your internal cost structures, profit margins, pricing strategies, and detailed five-year business plans are the roadmap to your success. In the wrong hands, this information is incredibly dangerous.
- Marketing and Sales Plans: That detailed strategy for an upcoming product launch—complete with target demographics, messaging, and media buying plans—is a prime example. If a leak would kill the impact of your launch, it almost certainly qualifies for protection.
The Value in Failure and "Negative Know-How"
One of the most powerful but overlooked areas for trade secret protection is what we call "negative know-how." This is all the knowledge you’ve gained from failed experiments and research dead-ends. Knowing what doesn't work can be just as valuable as knowing what does.
For example, imagine your company spent two years and $500,000 researching ten different material compositions for a new product, only to find they all failed. That list of ten failed compositions is a bona fide trade secret. It saves a competitor an immense amount of time and money by preventing them from going down the same blind alleys.
Documenting this kind of negative R&D is a critical part of a comprehensive trade secret inventory. It highlights just how broad the scope of protection can be. It’s not just about celebrating your wins; it's about safeguarding the entire body of knowledge your business has painstakingly built.
Taking the time to identify and document these assets now is the foundational step. It’s what makes your contracts, security measures, and—if it comes to it—legal enforcement truly effective.
If you want to discuss your business law matter, contact Kons Law at (860) 920-5181.
Building Your First Line of Defense with Contracts
Once you've mapped out what your trade secrets actually are, the next move is to wrap them in a layer of legal protection. Contracts are the absolute bedrock of any smart trade secret strategy. They create a clear, legally binding framework that tells everyone who touches your sensitive information exactly what the rules are.
Don't think of these agreements as just a formality. They are the foundational barrier standing between your competitive edge and the rest of the world. By having employees, contractors, and partners sign on the dotted line, you're putting them on formal notice: this information is confidential, and you can't use it or share it without permission. That simple act is incredibly powerful if you ever end up in court. One of the first things a judge will ask is whether you took "reasonable steps" to keep your secrets safe—and a well-drafted contract is your Exhibit A.
Anatomy of a Strong Non-Disclosure Agreement
The Non-Disclosure Agreement (NDA), or confidentiality agreement, is the go-to tool here. But here's the catch: not all NDAs are created equal. A generic template you pull off the internet probably won't cut it, especially in Connecticut where courts can be particular about how these agreements are written and enforced. A strong NDA has to be sharp, specific, and built for your business.
To be worth the paper it's printed on, an NDA needs to nail a few core components:
- Define "Confidential Information" with precision. Vague language like "all business information" is a recipe for disaster. Get specific. List out categories like "customer lists, marketing playbooks, financial projections, proprietary software source code, and unique manufacturing processes." The clearer you are, the harder it is for someone to later claim they didn't know something was protected.
- Outline the Scope of Permitted Use. The agreement has to spell out exactly why the other party is getting access and limit their use of the information to only that purpose. For instance, if you're talking to a potential investor, the scope should be locked down to "for the sole purpose of evaluating a potential investment in the company."
- Set the Duration of Confidentiality. How long does the obligation to keep the secret last? This could be a fixed period, like five years, or for true trade secrets, it can be indefinite—lasting as long as the information remains valuable and secret.
Getting these details wrong can make the whole agreement useless right when you need it most. For a deeper dive, it’s worth exploring the key elements that make up a truly effective non-disclosure agreement for employees.
Essential Agreements for Your Internal Team
While NDAs are great for outside parties, you need specific agreements for the people on the inside. Your employees and independent contractors are the ones with the deepest access to your crown jewels.
This is where a couple of key agreements come into play.
First is the Employee Confidentiality Agreement, which is often built right into the main employment contract. This creates a duty of confidentiality that lasts even after the employee walks out the door. It makes it crystal clear that any confidential information they work with or create on the job belongs to the company, period.
Second, you need an Intellectual Property (IP) Assignment Clause. This is a non-negotiable provision ensuring that any inventions, discoveries, or other IP an employee creates as part of their job automatically belongs to the company. Without it, an employee could develop a game-changing innovation on your dime, using your resources, and then walk away claiming they own it.
A solid confidentiality agreement is more than just a piece of paper; it's a carefully constructed legal shield. To be effective, it must contain specific clauses that clearly define the obligations of all parties involved. Below is a breakdown of the essential clauses that every business in Connecticut should consider including in their agreements.
Essential Clauses in a Confidentiality Agreement
| Clause Name | Purpose | Key Considerations for Connecticut Businesses |
|---|---|---|
| Parties | Clearly identifies who is disclosing information (Discloser) and who is receiving it (Recipient). | Ensure legal names and addresses are accurate. For LLCs or corporations, use the full registered business name. |
| Definition of Confidential Info | Specifically outlines what information is protected. | Be comprehensive but not overly broad. Connecticut courts prefer clear, specific definitions over vague catch-all phrases. |
| Recipient's Obligations | States the recipient’s duty to protect the information and not to disclose or use it for unauthorized purposes. | This is the core of the agreement. The language must be unambiguous about the duty of care and non-use. |
| Exclusions | Lists information that is not considered confidential (e.g., publicly known information, info already in the recipient's possession). | This clause adds reasonableness and can make the agreement more enforceable. It shows you aren't trying to overreach. |
| Return of Information | Requires the recipient to return or destroy all confidential materials upon request or at the end of the relationship. | Include a provision for certifying destruction, especially for digital files, which can be difficult to fully "return." |
| Term | Defines how long the confidentiality obligations will last. | For trade secrets, this should be indefinite. For other confidential data, a term of 3-5 years is common, but it must be reasonable for the industry. |
| Governing Law & Jurisdiction | Specifies that Connecticut law will govern the agreement and that any lawsuits must be filed in Connecticut courts. | This is crucial for creating predictability and avoiding having to litigate a dispute in an inconvenient or unfamiliar state court. |
| Remedies for Breach | Outlines the consequences of a breach, including the right to seek injunctive relief (a court order to stop the breach). | Including an injunctive relief clause acknowledges that monetary damages alone may not be enough to fix the harm from a disclosure. |
Making sure your agreements contain these clauses isn't just checking a box—it's about creating a document that will actually stand up and protect you when it matters.
Being proactive with these agreements is more than just good business hygiene; it's a critical defensive play. The cost of litigating trade secret theft in the U.S. is staggering, which is why prevention is always the better route for small and mid-sized businesses. Courts repeatedly emphasize that NDAs are 'critical' for proving a company took reasonable safeguards. Skipping them can kill your legal claim before it even gets off the ground. You can find more data on the high cost of trade secret litigation in this recent intellectual property law report.
Ultimately, these contracts are your first and most important line of defense. They set the rules of the game, create clear legal duties, and give you the proof you need to show that you value and actively protect your trade secrets.
If you want to discuss your business law matter, contact Kons Law at (860) 920-5181.
Implementing Practical Physical and Digital Safeguards
While contracts create a legal obligation to protect trade secrets, they’re only half the battle. If you ever have to go to court, a judge in Connecticut will want to see proof that you took "reasonable efforts" to maintain secrecy on your own. This means your day-to-day operational security has to back up the promises made in your legal agreements.
For many small and mid-sized businesses, this can sound expensive and complicated. The good news is that effective safeguards don't require a massive budget. It’s really about being smart, consistent, and intentional with both your physical space and your digital world.
Securing Your Physical Environment
Before we even get to the tech, let's talk about the physical world. Your most sensitive information often lives on paper, in prototypes, or within specific work areas. Controlling who can see and access these tangible assets is a foundational step.
Simple, low-cost measures can make a world of difference:
- Controlled Access: Does every employee really need access to every room? A simple keycard system or even just good old-fashioned locks can restrict entry to server rooms, R&D labs, or file storage areas.
- Secure Document Storage: Confidential papers shouldn't be left out on desks for anyone to see. Locked filing cabinets and a "clean desk" policy are basic but powerful habits that show you're serious about secrecy.
- Visitor Protocols: Every visitor needs to sign in and out. This log creates a clear record of who was in your building and when. More importantly, visitors should always be escorted and never left unattended in sensitive areas.
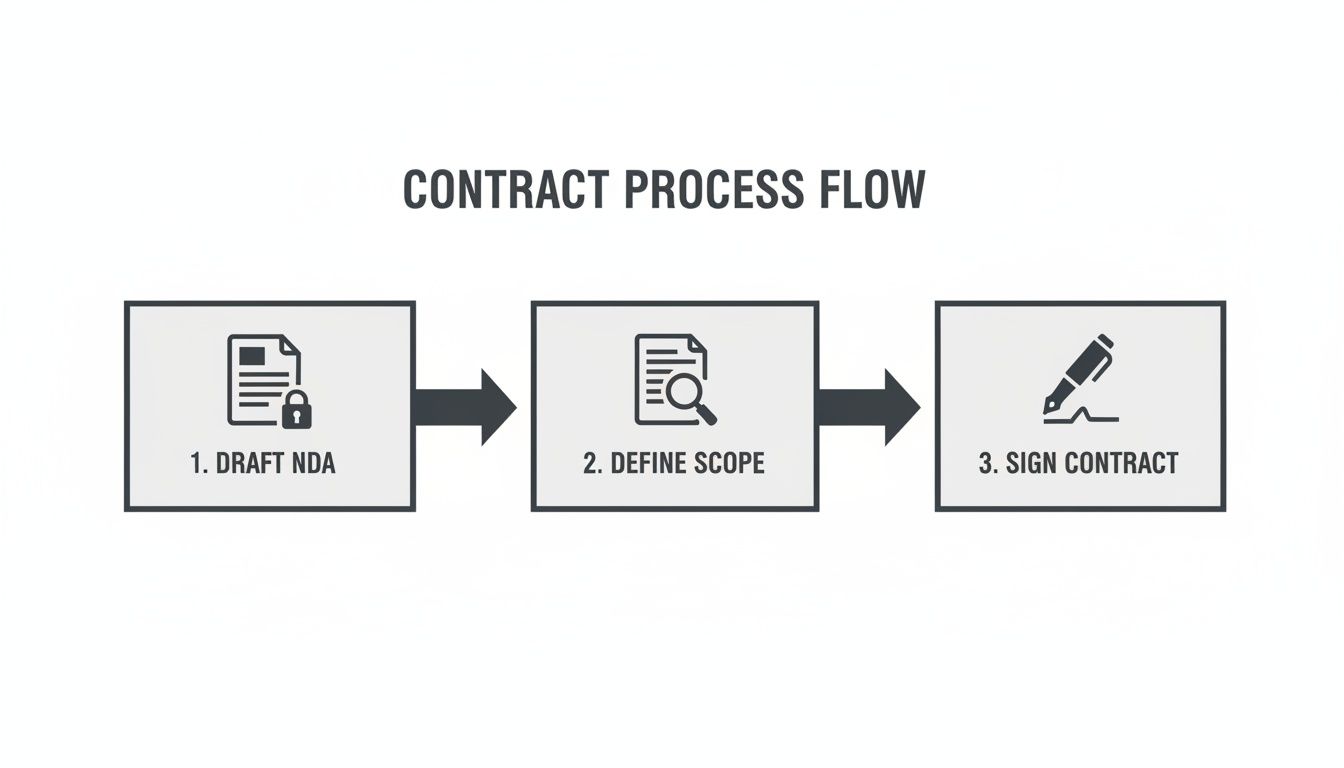
This kind of systematic approach—drafting NDAs, defining scope, and getting signatures—is the legal bedrock upon which all your other security measures should be built.
Bolstering Your Digital Defenses
In our connected world, the biggest threats are often digital. A single data breach can expose years of hard work in a flash. The goal is to create layers of security that make unauthorized access difficult and, just as importantly, detectable.
Your digital security posture should be built on a few core principles. You can find more in-depth information by exploring our articles on business security.
Access Control and Authentication
The principle of least privilege is your best friend here. It’s a simple idea: employees should only have access to the specific data and systems they absolutely need to do their jobs. A marketing intern, for example, has no reason to be in the folder containing your proprietary source code.
- User-Based Permissions: Implement role-based access controls on your network drives and cloud platforms.
- Strong Password Policies: Insist on complex passwords and make sure they’re changed regularly.
- Multi-Factor Authentication (MFA): This is one of the single most effective security measures you can implement, period. Requiring a second form of verification (like a code sent to a phone) makes a stolen password almost useless to a thief.
Remember, the ease with which electronic data can be captured and moved has fueled a boom in trade secret litigation. Simple digital hygiene like MFA is no longer optional; it's a critical component of the "reasonable efforts" standard that courts expect to see.
Data Encryption and Network Security
Think of encryption as scrambling your data so it can only be read by someone with the right key. It’s essential for protecting information both when it's just sitting on a server (at rest) and when it's being sent over a network (in transit).
- Encrypt Hard Drives: Any laptop or server holding confidential information should have its entire disk encrypted. That way, if a device is lost or stolen, the data on it remains unreadable.
- Use Secure Connections: Make sure all data transfers, especially over Wi-Fi, use encrypted protocols. This means HTTPS for websites and a VPN for anyone accessing the network remotely.
- Network Segmentation: Consider dividing your internal network into smaller, isolated segments. This way, if one part of the network is compromised, the breach is contained and can't easily spread to the servers holding your crown jewels.
By blending these practical physical and digital strategies, you build a comprehensive defense system. This layered approach not only helps you actively protect your trade secrets but also provides the tangible proof you’ll need to enforce your legal rights if a breach ever occurs.
If you want to discuss your business law matter, contact Kons Law at (860) 920-5181.
Navigating International Risks and Global Protection
Even if your business is firmly planted in Connecticut, the global economy means your trade secrets are always on the move. Every time you work with an international supplier, hire a contractor overseas, or even use foreign-made software, you’re opening a door to potential threats you might not have considered.
The legal protections you count on here in the U.S. simply don't have the same teeth across borders. This makes any international partnership a high-stakes game where your most valuable information is the prize.
While U.S. laws like the Defend Trade Secrets Act have some international reach, trying to enforce them in a foreign court can be a nightmare—it’s often slow, incredibly expensive, and sometimes, just plain impossible. The real work has to be done before you ever share a single sensitive file.
Vetting International Partners and High-Risk Zones
The first rule of going global? Know who you’re getting into business with. A potential partner’s home country matters—a lot. The strength of intellectual property (IP) law and, more importantly, the willingness to enforce it, varies wildly from place to place.
A deep, comprehensive vetting process is non-negotiable. This goes way beyond a simple background check. You need to dig into the potential partner's reputation for integrity, their current security setup, and the legal realities on the ground in their country. Our guide on the mergers and acquisitions due diligence checklist offers a great framework for this kind of investigation, even if you aren't in an M&A deal.
Some parts of the world are simply riskier than others when it comes to IP theft, and the U.S. government keeps a close watch on them. The U.S. Trade Representative's Special 301 Report, for example, recently put eight countries on its Priority Watch List: Argentina, Chile, China, India, Indonesia, Mexico, Russia, and Venezuela.
These countries were flagged for having serious gaps in their IP enforcement, which poses a direct threat to American businesses. For a Connecticut company, jumping into one of these markets without ironclad legal and practical safeguards is just asking for trouble. You can read more about these findings and the global challenges in protecting intellectual property on USTR.gov.
Structuring Stronger International Agreements
Your standard domestic contracts won't cut it when you're dealing with a foreign entity. You need agreements specifically built to handle cross-border risks and give you a clear path to take action if something goes wrong.
Make sure any international contract involving confidential information has these key clauses:
- Governing Law and Jurisdiction: This is your foundation. The contract must state that Connecticut and U.S. federal law govern the agreement. It should also specify that any legal fight has to happen in U.S. courts. It may not be perfectly enforceable in their country, but it's a critical line in the sand.
- Choice of Forum for Arbitration: Let's be realistic—foreign court systems can be unpredictable. International arbitration is often a better bet. Including a clause that requires arbitration in a neutral place like London or Geneva gives you a more level playing field.
- Audit Rights: You need the right to check their work. An audit clause gives you the contractual power to inspect a partner’s facilities and digital systems to make sure they're actually following the security rules you agreed on.
When you're protecting trade secrets abroad, you have to operate as if U.S. legal remedies are your absolute last resort. Your best defense is a smart combination of meticulous partner vetting and tough, well-drafted contracts that spell out clear obligations and serious consequences for any breach.
By approaching international business with a realistic view of the risks and a solid strategy to manage them, you can protect your company's crown jewels, no matter where in the world your partners are.
If you want to discuss your business law matter, contact Kons Law at (860) 920-5181.
Protecting Modern Assets Like AI Models and Proprietary Data
The idea of a company's "crown jewels" has fundamentally changed. Today, your most valuable assets might not be a secret formula locked in a vault or a piece of machinery on the factory floor. They’re more likely to be proprietary datasets and custom-built artificial intelligence (AI) models.
These modern, digital-native assets create entirely new challenges for trade secret protection.

Think about it: an AI algorithm isn't a physical object. It can be copied and distributed worldwide with just a few clicks. This reality makes all the traditional legal and security measures we've been discussing even more essential. For many modern businesses, the entire competitive advantage is wrapped up in the code, architecture, and training data of their AI systems.
Why Trade Secret Protection is Ideal for AI
When business owners think about protecting an invention, their first thought is often patents. But for AI and machine learning models, that can be a huge strategic mistake.
The patent process requires you to publicly disclose, in painstaking detail, exactly how your invention works. You’re essentially handing your competitors the blueprint to your most valuable asset.
Trade secret law offers a much more powerful alternative because its entire purpose is built on maintaining secrecy. By treating your AI model as a trade secret, you can protect it forever—as long as it stays confidential and continues to give you a competitive edge. You get all the legal protection without having to show your hand to the public.
Unique Protective Measures for Digital Assets
Guarding digital-native secrets isn't as simple as locking the server room door. It demands a sophisticated blend of technical safeguards and sharp legal strategy to secure the code and data itself.
You need to focus on a few key areas:
- Software Hardening: Your code needs its own armor. This means implementing technical measures that make it incredibly difficult for anyone to reverse-engineer your software or figure out the underlying model by running repeated queries against it.
- Documenting Competitive Advantage: Just like with any other trade secret, you have to be able to prove its value. Meticulously document how your specific algorithm or dataset gives you a real, tangible advantage. Is it faster? More accurate? Does it solve a problem no one else can?
- Controlling Training Data: The data you use to train an AI model is often a valuable trade secret on its own. Use rock-solid contracts and strict access controls to manage how that data is used, stored, and shared, especially when you’re working with third-party data providers or contractors.
Trade secrets have surged as the primary shield for AI innovations, easily outpacing patents that require full disclosure. Courts are reinforcing their global enforceability but demand rigorous protections, such as precise asset definition and hardened software interfaces to prevent extraction attacks. You can learn more from a recent analysis on AI and trade secret law.
Ultimately, safeguarding assets like AI models requires a forward-thinking approach. By pairing robust cybersecurity with the durable, privacy-focused protection of trade secret law, you can make sure your most important digital innovations remain a source of lasting competitive strength.
If you want to discuss your business law matter, contact Kons Law at (860) 920-5181.
Responding Strategically When a Breach Occurs
That sinking feeling in your stomach when you suspect a trade secret has been stolen is something no business owner wants to experience. But in that critical moment, panic is your worst enemy. The key is to act with precision and speed, because a swift, strategic response can mean the difference between containing the damage and losing your competitive edge.
Your first move isn't to start pointing fingers or firing people. It's to quietly launch an internal investigation while locking down every piece of potential evidence. This means immediately securing laptops, servers, access logs, and any communications tied to the suspected breach. Do not wipe devices or delete files. That can be viewed as destroying evidence and will seriously hamstring your legal case later on. Instead, think like a detective and create forensic images of all relevant hard drives.
Engaging Legal Counsel Immediately
This is not a do-it-yourself project. Getting an experienced trade secret attorney involved from the very beginning is the single most important step you can take. Your lawyer can direct the investigation under attorney-client privilege, which helps shield the findings from being disclosed. They'll also be your guide through the complexities of federal and state law.
Both the federal Defend Trade Secrets Act (DTSA) and Connecticut's Uniform Trade Secrets Act (CUTSA) give victims of trade secret theft powerful legal tools. An attorney can quickly size up the situation and tell you if you have grounds to seek immediate court intervention, like a Temporary Restraining Order (TRO). A TRO can be a game-changer, stopping the thief in their tracks and preventing them from using or sharing your valuable information any further. When theft and complex disputes are involved, truly understanding the landscape of business litigation law is absolutely essential.
Understanding Your Legal Remedies
If you can prove your trade secret was misappropriated, the law provides real teeth to make your business whole again. The goal isn't just to punish the wrongdoer; it's to compensate you for the harm and make sure they don't profit from their illegal actions.
Under both the DTSA and CUTSA, you may be entitled to recover damages for your actual losses, such as lost profits, as well as any profits the misappropriating party gained from their unjust enrichment. In cases of willful and malicious theft, courts may even award exemplary damages—up to twice the amount of actual damages—and attorney's fees.
Acting decisively, with solid legal guidance, is what maximizes your chances of mitigating the damage and holding the responsible parties accountable. It's about turning a defensive reaction into a proactive legal strategy to protect what you've built.
If you want to discuss your business law matter, contact Kons Law at (860) 920-5181.
Common Questions About Protecting Trade Secrets
When it comes to your company's intellectual property, knowing which legal tool to use for the job is half the battle. People often get trade secrets, patents, and copyrights confused, but each one protects something very different.
Think of it this way:
- Trade Secrets: This is your secret sauce. It's the confidential information—a customer list, a unique manufacturing process, a chemical formula—that gives you an edge precisely because no one else knows it. As long as you keep it secret and it has value, it's protected.
- Patents: These are for new inventions, like a machine or a software process. To get a patent, you have to tell the world exactly how your invention works in exchange for a temporary monopoly, usually 20 years.
- Copyrights: This is for creative expression. It covers things like your website's code, marketing brochures, and blog posts. Copyright protects the way an idea is expressed, not the underlying idea itself.
How Long Does Trade Secret Protection Last?
Here’s where trade secrets really shine: their protection can theoretically last forever. Unlike patents that expire, a trade secret remains legally protected as long as it stays confidential and continues to provide economic value.
But there’s a catch. If that information ever becomes public knowledge—whether through a leak, a careless employee, or someone else figuring it out on their own—the trade secret is gone for good. That’s why consistent, robust security measures aren't just a good idea; they're an absolute necessity.
Protecting Ideas When Pitching to Investors
This is a scenario every founder faces. You have to reveal enough to get an investor excited, but you can’t just give away the keys to the kingdom. The answer is a rock-solid Non-Disclosure Agreement (NDA).
Before you dive into the details of your proprietary tech or unique business model, get the potential investor to sign a well-drafted NDA. This creates a legal obligation for them to keep your information confidential and gives you a clear path to a remedy if they misuse it.
It's standard professional practice. Handing an investor an NDA shows you’re serious about protecting your IP and turns a high-stakes pitch into a secure, productive business conversation.
Protecting your company’s most valuable assets requires careful legal planning. If you want to discuss your business law matter, contact Kons Law at (860) 920-5181.
