A lot of Connecticut business owners already have trade secrets. They just don't label them that way.
It might be a custom quoting method in a machine shop, a supplier list built over years, a customer retention playbook in a service company, a formulation in a food business, or an internal workflow that cuts waste and keeps margins healthy. Those assets often sit in shared folders, live in an owner's head, or move too freely between employees, vendors, and devices. That's where risk starts.
The importance of trade secret protection isn't academic. It's practical. If information gives your business an edge because other people don't know it, and if you treat it like confidential property, the law may protect it. If you don't treat it that way, you may lose that protection when you need it most.
Your Business's Most Valuable Hidden Asset
A Connecticut business doesn't need to be a biotech company or software startup to own a valuable secret. A local bakery may rely on a recipe and production method that keeps customers coming back. A specialty manufacturer may have a finishing process that reduces defects. A distributor may know which pricing terms, reorder timing, and service touches keep major accounts from shopping competitors.
That kind of know-how is often more valuable than the owner realizes, because it's woven into daily operations instead of hanging on the wall as a certificate.

The data backs up what many business lawyers see in practice. A detailed survey by the National Science Foundation found that 56.2% of small firms with fewer than 500 employees considered trade secrets “very important” to their business, a higher share than those prioritizing patents, trademarks, or copyrights according to this NSF and BRDIS trade secret analysis.
What business owners often miss
Many owners think of intellectual property as something formal and registered. They think of patents filed in Washington or trademarks approved by the USPTO. Trade secrets work differently. They can exist inside ordinary business records and operating habits.
Common examples include:
- Customer intelligence that shows buying patterns, renewal cycles, and preferred terms
- Internal pricing logic that helps protect margins without losing bids
- Operational methods that reduce scrap, delay, rework, or returns
- Vendor and sourcing information that gives access to better inputs or better timing
- Sales scripts and service playbooks that consistently convert and retain clients
A business usually loses a trade secret long before a lawsuit starts. It loses it when confidentiality becomes casual.
That's why the first step isn't filing something. It's identifying what matters. Businesses that want a practical starting point can review this overview on protecting trade secrets and then compare it against how information really flows through their company.
Why this matters in Connecticut
Connecticut companies tend to operate with lean teams. People wear multiple hats. Founders share information quickly so work gets done. That helps growth, but it can weaken legal protection if sensitive information is never classified, never limited, and never backed by written agreements.
A hidden asset stays valuable only if the business handles it like an asset.
What Legally Constitutes a Trade Secret
Not every confidential fact is a trade secret. “Private” and “protected” aren't the same thing.
At a practical level, trade secret law asks three basic questions. Does the information have economic value because it isn't generally known? Is it secret from outsiders? Has the business taken reasonable steps to keep it secret?
The three legal features that matter
In technology, trade secrets can protect proprietary algorithms and AI models indefinitely, unlike patents, which have a 20-year limit, as explained in this trade secret guide for algorithms and AI models. That same source also points to the operational side of protection: the information must derive value from secrecy, and the owner must use reasonable measures such as role-based access controls and NDAs.
Those principles apply far beyond software.
A trade secret can be:
- Technical information such as formulas, code, manufacturing parameters, testing methods, or calibration settings
- Commercial information such as pricing models, bid strategy, profit assumptions, or customer segmentation
- Operational know-how such as onboarding procedures, logistics methods, or quality control sequences
- Negative know-how such as failed approaches that save your team from repeating expensive mistakes
What counts as reasonable efforts
Courts don't expect perfection. They do expect discipline.
If a company says information is secret but stores it in an open shared drive, discusses it freely with vendors, and never uses confidentiality language in contracts, that company has a problem. On the other hand, a business that labels sensitive files, limits access by job role, uses NDAs, retrieves devices, and trains employees has a stronger argument that it treated the information as a trade secret.
Practical rule: If everyone can access it, copy it, or take it with them, it probably won't be treated like a trade secret later.
Examples by industry
Here's how this looks in ordinary Connecticut businesses:
- Manufacturer: machine settings, tolerances, sequencing, sourcing terms, inspection methods
- Professional services firm: proposal templates, pricing logic, customer churn triggers, referral systems
- Food or beverage company: formulations, shelf-life methods, blending steps, supplier relationships
- Software or SaaS business: models, prompts, training pipelines, architecture choices, deployment workflows
- Distributor or wholesaler: account histories, rebate terms, fulfillment logic, territory strategy
The legal test is simple to say and hard to fake. The information must be valuable because it's not generally known, and the business must behave like secrecy matters.
Why Trade Secrets Drive Competitive Advantage
For many small and mid-sized businesses, trade secrets are the most practical form of intellectual property because they protect what creates day-to-day advantage. Not branding. Not an invention described in a filing cabinet. The systems and information that help the company sell better, source better, and operate better.
That business reality shows up in valuation. By 2009, trade secrets were estimated to comprise up to 81% of a company's total value in knowledge-intensive industries, according to this analysis of the growing importance of trade secrets.

What makes trade secrets powerful
Trade secrets have several advantages that business owners care about immediately.
- No registration delay: Protection can begin without waiting for a government office to issue a registration.
- No public disclosure requirement: You don't have to publish the details of your process to get protection.
- Broad coverage: Trade secrets can cover business methods, commercial information, and know-how that patents and trademarks don't fit well.
- Potentially ongoing duration: Protection can continue as long as secrecy is preserved.
That last point is where the importance of trade secret strategy really becomes clear. A patented invention eventually expires. A trademark protects source identity, not internal know-how. A trade secret can keep protecting the confidential method itself, if the business maintains control.
The real trade-off
Trade secrets aren't magic. They don't protect against independent invention or lawful reverse engineering. If a competitor can figure out the method without stealing or breaching confidence, trade secret law may not stop them.
That means this tool works best when the edge is difficult to observe from the outside. Internal pricing systems, customer analytics, sourcing terms, manufacturing tolerances, software workflows, and back-office operational logic are often better candidates than product features visible to the public.
The strongest trade secret is usually the one competitors can't see, customers don't need disclosed, and employees can access only on a need-to-know basis.
For many Connecticut companies, the best strategy isn't choosing trade secrets instead of all other IP. It's deciding which assets should remain confidential because secrecy gives them more value than disclosure would.
The Legal Framework Protecting Connecticut Businesses
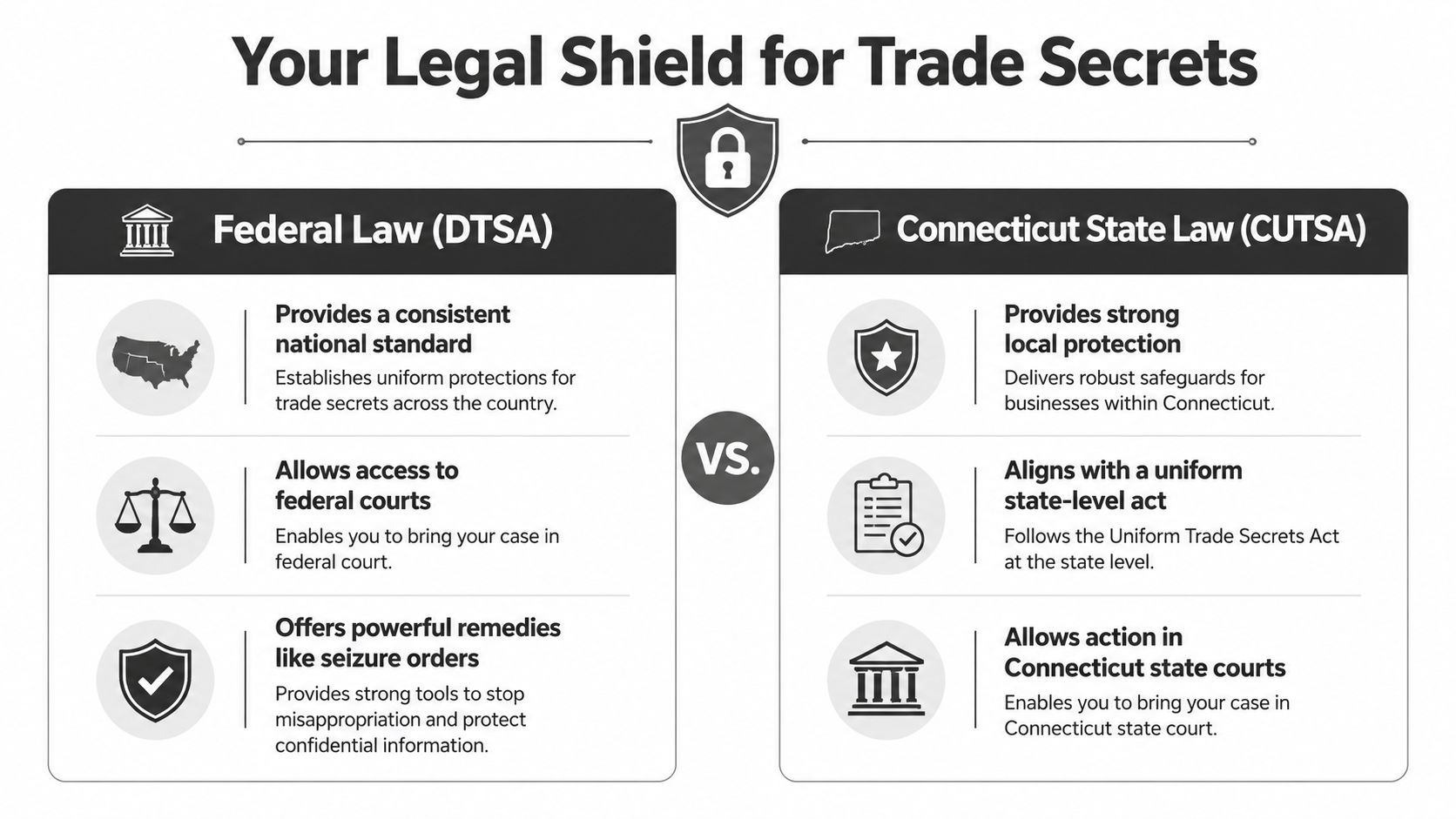
Connecticut businesses usually operate under two layers of trade secret protection. One is federal. The other is state.
At the federal level, the Defend Trade Secrets Act, often called the DTSA, allows certain trade secret claims to be brought in federal court. At the state level, Connecticut has its own version of the Uniform Trade Secrets Act, commonly called CUTSA. Together, they give business owners legal tools when someone steals, discloses, or uses protected confidential information without authorization.
What misappropriation means in plain English
Misappropriation generally means improper acquisition, disclosure, or use of a trade secret. In ordinary business terms, that can include an employee emailing confidential files to a personal account before resigning, a former manager using a protected customer list at a competing firm, or a vendor passing along restricted process information in violation of a contract.
The key issue is usually not whether the information was useful. It's whether the business treated it as secret and whether the other party got or used it improperly.
What these laws allow you to seek
If a trade secret has been misappropriated, a business may be able to seek court orders to stop further use or disclosure. It may also pursue money damages and other relief depending on the facts.
That matters because speed often decides the outcome. Once confidential information spreads, practical recovery becomes harder even if the legal claim is strong. Businesses that move quickly tend to preserve more options than those that wait, investigate informally for months, and let evidence disappear.
A useful starting point for owners who want a broader legal backdrop is this summary of Connecticut business laws, especially if trade secret issues overlap with employment, contract, ownership, or transaction questions.
Good enforcement starts before any breach. Courts look backward at the security steps you had in place, not the steps you wish you had adopted after the leak.
Why state and federal alignment matters
The practical benefit of having both federal and Connecticut remedies is flexibility. Depending on the dispute, the parties, and the evidence, counsel can evaluate the best forum and the strongest claims. But no statute rescues a business that was careless with secrecy from the start.
That's why legal protection and operational discipline have to work together.
Comparing Trade Secrets Patents and Trademarks
Business owners often ask a fair question. If information is valuable, should it be treated as a trade secret, patented, or branded through a trademark strategy?
The answer depends on what the asset is, how visible it is, how long it will matter, and whether public disclosure helps or hurts the business.
For readers dealing with reputation-sensitive brands or personalities, this resource on IP solutions for public figures is also useful because it shows how intellectual property choices can change depending on visibility and enforcement goals.
Intellectual Property at a Glance Trade Secret vs. Patent vs. Trademark
| Attribute | Trade Secret | Patent (Utility) | Trademark |
|---|---|---|---|
| What it protects | Confidential business information, know-how, methods, data, processes | New and qualifying inventions | Brand names, logos, slogans, source identifiers |
| Core requirement | Economic value from secrecy plus reasonable secrecy measures | Patentable subject matter and formal application process | Use in commerce to identify source |
| Public disclosure | No, secrecy is the point | Yes, the invention is disclosed in the patent filing | Public-facing by design |
| Duration | Potentially indefinite while secrecy lasts | Limited term | Can continue if properly maintained and used |
| Cost profile | Often lower on the front end, but requires internal controls | Higher filing and prosecution burden | Moderate and usually tied to clearance, filing, and policing |
| Weak point | Lost if secrecy is lost or if others lawfully develop it independently | Expires after the patent term | Doesn't protect internal know-how |
Choosing the right tool
If your value sits in a formula, internal process, customer data set, or pricing method that outsiders can't easily observe, trade secret treatment may make sense.
If your innovation will be visible in the product itself and competitors can lawfully reverse engineer it, patent analysis becomes more important.
If your concern is market recognition and customer confusion, trademark law is the right lane.
Many businesses need all three. A software company may protect code and models as trade secrets, patent certain technical features, and register the product name as a trademark. A manufacturer may rely on secret tolerances and supplier methods while separately protecting a brand line.
For a broader view of how these rights fit together, this overview on how to protect intellectual property gives a useful framework.
Practical Steps to Safeguard Your Business Secrets
Most businesses don't lose trade secrets because the law is weak. They lose them because the company never translated “this matters” into repeatable procedures.
That gap is common. The World Intellectual Property Organization notes a significant implementation problem: roughly 75% of enterprises recognize trade secrets as important, about 40% don't use any trade secret-related services, and half are unfamiliar with their jurisdiction's laws, as described in this WIPO guide on trade secrets and innovation.

Start with an internal trade secret audit
Don't begin with forms. Begin with inventory.
Ask department heads what information would hurt the business if a competitor received it today. Then sort that information into categories such as customer data, pricing, operations, product development, sourcing, software, and financial modeling.
A useful audit usually answers four questions:
- What is the asset
- Why does secrecy create value
- Who currently has access
- What controls already exist
This exercise often reveals that the business has been treating high-value information and ordinary information the same way.
Tighten contracts and employment documents
Your documents should match your expectations. If you expect confidentiality, say so clearly.
That often includes:
- Employee confidentiality clauses that define protected information and surviving obligations after employment ends
- Standalone NDAs for contractors, consultants, vendors, and deal discussions
- Offer letter and handbook language about ownership of work product, device return, and records retention
- Exit procedures that confirm return of company property and remind departing personnel of continuing duties
A practical reference point for this issue is this explanation of employee non-disclosure agreements.
Limit access like you mean it
A trade secret shouldn't sit in a folder accessible to everyone with a company login.
Use role-based access. Segment files by function. Restrict downloads where appropriate. Remove access promptly when roles change. For physical materials, use locked storage, visitor limits, and clean-desk expectations for sensitive records.
Businesses reviewing their technical controls may also find this Guide to business data protection helpful, especially when confidentiality depends on secure handling of digital information.
If a company can't identify who had access to a secret, it will struggle to prove the secret was actually controlled.
Train people and rehearse the response
Policies no one understands won't help much in a dispute. Employees should know what the company considers confidential, where it's stored, how it may be shared, and what to do when a customer, vendor, or former coworker asks for something they shouldn't provide.
The same goes for incident response. When a business suspects copying or disclosure, it needs a plan for preserving evidence, securing systems, stopping further spread, and getting legal advice quickly.
Enforcement and Your Actionable Protection Checklist
When misappropriation happens, the immediate goal is usually containment. Stop the use. Stop the disclosure. Preserve evidence. Then assess what claims, contracts, and remedies apply.
Trade secret enforcement can include requests for injunctions and claims for financial relief, but those remedies work best when the business can show a court that it treated the information as protected property before the dispute started. Judges notice the basics. Written policies, restricted access, signed agreements, exit steps, and documented training all help.
A practical checklist for Connecticut businesses
Use this as a working list, not a one-time project.
- Identify the assets: List the information that gives your business an edge because competitors don't have it.
- Classify sensitive material: Mark categories of confidential and trade secret information in a consistent way.
- Review agreements: Update employee, contractor, vendor, and deal documents to include workable confidentiality terms.
- Control access: Limit files, systems, and physical materials to people with a legitimate need to know.
- Train managers and staff: Explain what counts as confidential and how disclosure can happen in ordinary workflows.
- Run departure procedures: Cut off access, collect devices, confirm return of records, and remind departing personnel of ongoing obligations.
- Prepare for breach response: Know who will handle legal review, forensic preservation, internal communication, and court action if needed.
The businesses in the best position to enforce rights are usually the ones that treated confidentiality as an operating system, not a formality.
If your company has valuable methods, data, pricing logic, or customer intelligence, now is the right time to test whether your current practices would hold up under scrutiny.
If you want to discuss your business law matter, contact Kons Law at (860) 920-5181.
