Preventing business fraud isn’t about just one thing. It's about building a layered defense with strong internal controls, smart employee training, and rigorous vendor verification. This isn't just about playing defense; it’s a proactive strategy designed to spot and shut down fraud before it costs you money and damages your reputation.
The Real Cost of Business Fraud Today
It's easy to think of fraud as an abstract threat, but the risks are immediate and very real for businesses right now. Schemes like Business Email Compromise (BEC) and vendor impersonation aren't rare, sophisticated attacks anymore. They’re common tactics that are frighteningly good at slipping past standard security.
These aren't just IT problems. They are fundamental business and legal challenges that can drain your cash flow, destroy client trust, and threaten the stability you've worked so hard to build.
The reality is that fraud is everywhere, and getting your money back is a long shot. An astonishing 79% of organizations worldwide were targeted by payments fraud attacks or attempts. That number alone should tell you how urgent this is.
The most common culprit? BEC. Fraudsters are impersonating third parties (63% of cases), vendors (60%), and even senior executives to trick well-meaning employees into sending money to the wrong accounts. You can see the latest payment fraud trends and get a sense of just how quickly this threat is evolving.
The Financial Fallout of a Successful Attack
For a small or mid-sized business, a single successful fraud attack can be catastrophic. Once funds are wired to a criminal’s account, the chances of ever seeing that money again are slim.
In fact, recovery rates are dropping fast. Only 22% of organizations managed to get back 75% or more of the funds they lost to fraud. That's a huge drop from the previous year, when 41% of businesses reported similar success. The takeaway here is crystal clear: prevention is infinitely more effective than recovery.
The modern fraud environment operates on speed and deception. Once money is wired to a fraudulent account, it is often moved through multiple international banks within hours, making it nearly impossible to trace and reclaim.
Beyond the Balance Sheet: The Hidden Damages
The direct financial loss is painful, but the ripple effects can be just as damaging. A major fraud incident can shatter client confidence, tarnish your brand, and pull you into expensive, time-consuming legal fights.
Internally, it creates chaos. You're forced to launch investigations, pull people away from their real jobs, and divert critical resources from growing your business.
For companies that handle sensitive data or financial transactions, fraud can also create a regulatory and compliance nightmare. These situations can sometimes bleed into other complex legal issues. You can learn more about how deception impacts financial markets by reading our guide on what is securities fraud.
Ultimately, a strong anti-fraud program isn't just about protecting your bank account—it's about protecting your entire business. If you want to discuss your business law matter, contact Kons Law at (860) 920-5181. In the sections that follow, we'll lay out a practical blueprint for building the defenses you need.
Building Your First Line of Defense
After seeing how devastating fraud can be, the only logical step is to build a proactive defense. The cornerstone of that defense is a solid set of internal controls to prevent fraud. These aren't just about creating red tape; they are the practical, everyday checks and balances that guard your assets and ensure your financial reporting is honest.
For small and mid-sized companies especially, these controls are the bedrock of fraud prevention.
Think of it this way: you want to design a system where no single person holds all the keys to the kingdom. This core principle, segregation of duties, is one of the most effective tools you have. It simply means dividing critical financial tasks among different people, which creates a natural and powerful system of accountability.
This is why it's so important. The typical fraud scheme often starts small but ends with a painful reality.
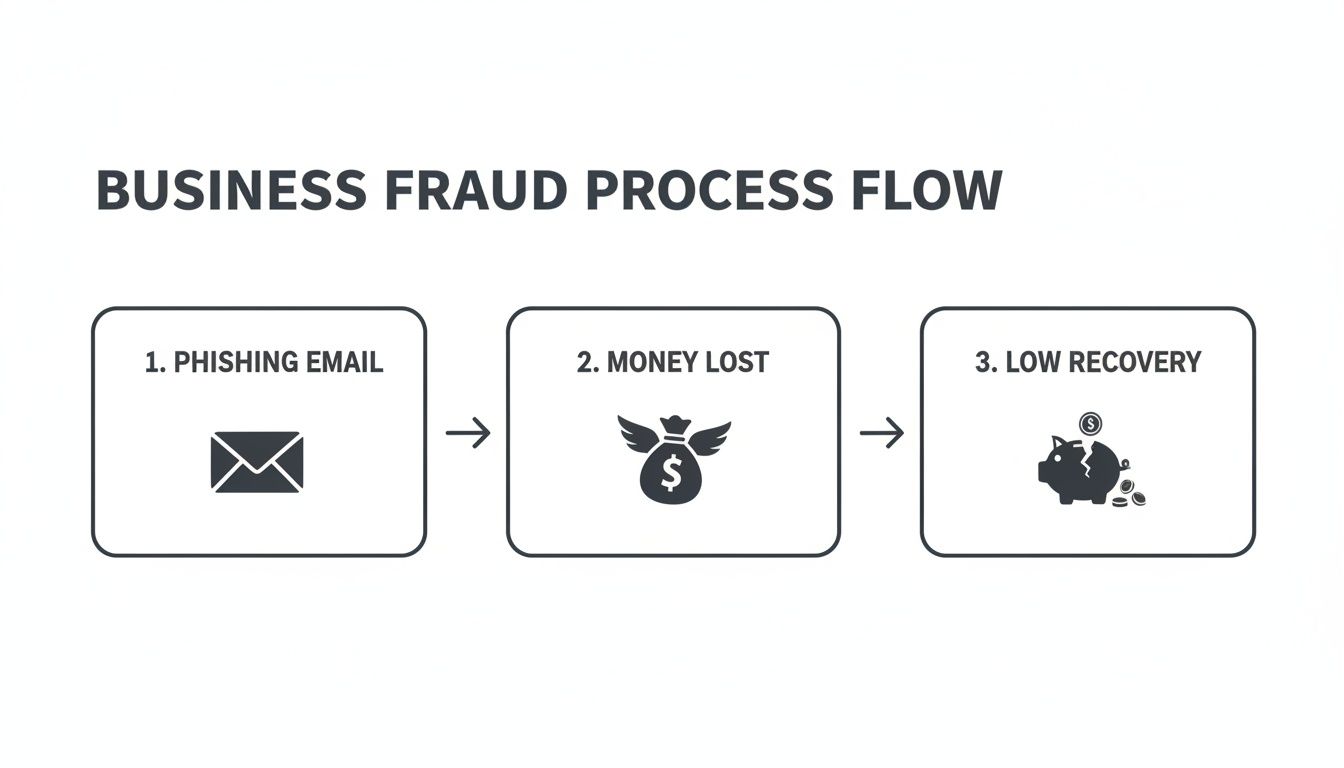
As you can see, once the money is gone, the odds of getting it back are slim. Prevention is really your only viable strategy.
Implementing Essential Financial Controls
Segregation of duties is the starting point, but a strong defense needs more layers. You should weave these controls directly into your day-to-day financial processes so they become second nature, not a special exception.
Here are a few non-negotiable controls every business should implement:
- Dual Signature Requirement: For any check or wire transfer over a set amount—say, $5,000—mandate signatures from two authorized people. This simple step prevents one person from unilaterally moving significant funds.
- Independent Bank Reconciliation: The person handling daily bookkeeping should never be the one reconciling the monthly bank statements. This job needs to go to a different employee, an owner, or an outside accountant to get a fresh, unbiased set of eyes on every transaction.
- Mandatory Paid Time Off: This one might surprise you. Requiring employees in financial roles to take at least one full week of consecutive vacation can be incredibly revealing. Most fraud schemes require constant upkeep, and an employee's forced absence can cause the whole thing to unravel.
A common mistake is thinking that trust is a substitute for control. The point of internal controls isn't to show you distrust your team; it's to protect honest employees from temptation and suspicion while removing the opportunity for anyone to do the wrong thing.
Comparing Weak vs. Strong Internal Controls
Seeing the difference between a vulnerable process and a secure one can be eye-opening. Many businesses, especially smaller ones, operate with weak controls without realizing the risk they're taking.
The table below contrasts common high-risk practices with the stronger, more secure alternatives you should aim for.
| Business Area | Weak Control (High Risk) | Strong Control (Low Risk) |
|---|---|---|
| Vendor Payments | One employee can add a new vendor, approve their invoice, and issue payment. | The A/P clerk enters invoices, but a separate manager must approve them. Adding a new vendor requires manager sign-off and verification of bank details. |
| Bank Reconciliation | The bookkeeper who writes checks and makes deposits also reconciles the bank statements. | A manager or owner who does not handle daily transactions reconciles the bank statements monthly. |
| Expense Reports | Employees approve their own expense reports, or their direct reports approve them. | All expense reports are approved by a supervisor at least one level above the employee and are reviewed for policy compliance. |
| Cash Handling | A single cashier handles all cash, prepares the deposit, and takes it to the bank. | Two employees count cash together. One prepares the deposit slip, and another person (e.g., a manager) verifies it and takes it to the bank. |
Implementing these stronger controls closes the gaps that fraudsters love to exploit. It's about creating a system of deliberate checks and balances.
From Theory to Action: A Checklist for Your Operations
To find your company’s unique weak spots, you need to take a hard, honest look at your current processes. This isn't about placing blame; it's about finding vulnerabilities before someone else does.
Use these questions as a starting point to audit your own operations:
- Who has the authority to initiate payments?
- Who approves those payments?
- Is it the same person doing both?
- Who has access to company bank accounts and credit cards?
- Who reconciles those accounts every month?
- What’s the process for adding a new vendor to your system?
- How do you verify a request to change a vendor’s banking information?
If your answers show that one person controls a financial process from beginning to end, you've just found a critical vulnerability. The goal is to insert a check or a balance at every key point. For more on building a comprehensive framework, our guide on a corporate compliance program can help structure your anti-fraud efforts.
The Power of Surprise Audits
Even with great daily controls, periodic and unannounced audits act as a powerful deterrent. These don't have to be massive, formal events. A surprise audit can be as simple as an owner randomly reviewing a week's worth of expense reports or doing a spot-check on petty cash.
The psychological impact is huge. When people know their work could be reviewed at any time, it reinforces accountability and discourages them from trying to bend the rules. It sends a clear message: we are always watching.
Putting these defenses in place requires thoughtful planning and consistent enforcement. If you want to discuss your business law matter, contact Kons Law at (860) 920-5181. Properly implemented controls are your best insurance policy against both internal and external threats, securing your company’s financial future.
5. Screen, Train, and Protect Against Human Risk
Your most robust financial controls and sophisticated software can be completely undermined by one critical variable: people.
I’ve seen it happen time and again. A company invests in top-tier security, only to have it all bypassed because an employee clicked a convincing-looking link. Preventing business fraud requires a laser focus on the human element, because both intentional and unintentional actions from employees and vendors are often the root cause of the most significant losses.
Managing this "human risk" goes far beyond a simple background check. It's about building a vigilant, security-conscious culture from the inside out.

The reality is that people are the primary targets of most modern fraud schemes. Attackers don't just hack systems; they manipulate your team through clever social engineering and phishing attacks designed to exploit trust and urgency. This is why ongoing, practical training isn't a "nice-to-have"—it's an essential layer of your defense.
Cultivate an Aware and Empowered Team
A one-time training session during onboarding just won't cut it. Fraud tactics evolve constantly, so your training has to be a continuous process. The goal is to move your employees from passive awareness to active defense.
Here’s how you can build that defensive mindset:
- Run Simulated Phishing Attacks: Regularly send controlled, fake phishing emails to your staff. These tests are invaluable for helping employees learn to spot red flags—like suspicious links, urgent demands for sensitive information, and unusual sender addresses—in a safe, no-consequence environment.
- Teach Social Engineering Tactics: Educate your team on common manipulation tricks, like pretexting (creating a fake story to gain trust) or baiting (offering something enticing to trick someone). Use real-world examples to make the threat tangible and memorable.
- Create Clear Reporting Channels: You need an easy and confidential way for employees to report anything suspicious without fear of blame. Whether it's a strange email or an odd payment request, they should feel completely empowered to raise a hand and ask, "Does this seem right?"
A positive work culture where employees feel valued is a powerful anti-fraud tool. When people feel like they are part of the mission to protect the company, they are far more likely to be vigilant and speak up when something feels off.
Fortify Your Vendor Relationships
Your third-party vendors and partners represent another massive source of risk. A weak link in your supply chain can expose you to everything from invoice fraud to devastating data breaches. A solid fraud prevention plan must extend beyond your own four walls.
Before entering into any new partnership, you absolutely have to conduct thorough due diligence. This isn't about distrust; it's about responsible business practice.
- Verify Credentials: Don't just take a new vendor at their word. Independently verify their business registration, check for professional licenses, and look for online reviews or references from other clients in your network.
- Confirm Bank Details: This one is critical. When setting up a new vendor for payment, implement a multi-step verification process. This must include a phone call to a known, trusted number (not one from an email) to confirm account information before a single dollar is sent.
Embed Protection Directly into Your Contracts
Your contracts are more than just agreements; they are legal shields. Embedding specific anti-fraud clauses into your vendor and partner agreements is a critical step in managing third-party risk. These clauses set clear expectations and provide legal recourse if something goes wrong.
Consider insisting on these provisions:
- Right to Audit: Include a clause giving you the right to audit the vendor's records related to your account. This is a powerful deterrent and allows you to investigate if you suspect overbilling or other fraudulent activity.
- Data Security Standards: Require vendors to adhere to specific data security and privacy standards, especially if they handle your sensitive customer or financial information.
- Fraud Reporting Obligation: Mandate that the vendor must immediately notify you of any suspected or confirmed fraudulent activity that could impact your business.
Structuring agreements with this level of detail is crucial. For guidance on creating strong, protective agreements, many of the same principles of clarity and protection found in an employment agreement review apply here as well. This proactive legal approach ensures that if a partner's negligence leads to a loss, you have a clear path to hold them accountable.
If you want to discuss your business law matter, contact Kons Law at (860) 920-5181.
6. Using Technology for Smarter Fraud Detection
While strong internal controls and vigilant employees are the bedrock of any anti-fraud strategy, technology is the force multiplier that lets you see the whole picture. It helps you monitor transactions at scale and spot red flags in real-time, moving your business beyond manual checks that can only catch so much.
The good news? You don't need a massive IT department or a six-figure budget to get started. Many of the tools you already use—especially your accounting software—have powerful fraud detection features built right in. The key is simply knowing they exist and taking the time to turn them on.

Leveraging Your Existing Software
Modern accounting platforms are designed to do far more than just balance the books. Think of them as data hubs that can be set up to automatically flag suspicious activities that often point to fraud. The goal is to create a system of automated alerts that bring potential issues to you immediately, not weeks or months down the road during an audit.
Start by digging into your software's notification settings. You can set up alerts for specific, high-risk scenarios that warrant a closer look:
- Unusual Transaction Times: Get an alert for any payments or invoices created or approved outside of normal business hours. A payment pushed through at 2:00 AM on a Sunday should raise some questions.
- Duplicate Invoices: Set a rule to flag any invoice number that matches one you've already paid. It’s a simple but incredibly effective way to catch both accidental and intentional double payments.
- New Vendor Payments: Create a notification for the very first payment made to a new vendor. This gives you a critical window to verify that the vendor is legitimate and the banking details are correct before any money leaves your account.
- Changes to Bank Details: This one is non-negotiable. Any modification to a vendor's or employee's bank account information must trigger an immediate, high-priority alert that requires manual sign-off.
Technology should be your tireless watchdog. Its job is to sift through the noise of daily transactions and highlight the few anomalies that truly need a human's critical review. It makes your manual checks more targeted and far more effective.
The Power of Multi-Factor Authentication
If there is one single technological control you implement, make it multi-factor authentication (MFA). It’s a simple concept: requiring a user to provide two or more verification factors to get in, like their password plus a one-time code sent to their phone.
Enforcing MFA on every system that touches your finances—your bank portals, accounting software, and payment processors—is one of the most powerful steps you can take. It effectively neutralizes the threat of stolen passwords, a primary tool criminals use to take over accounts. It’s a low-cost measure with a massive security payoff.
The financial world is grappling with this reality as consumer fraud losses have soared past $12.5 billion. A key lesson here is that catching fraud early is everything. While about a third of institutions catch fraud during onboarding, the rest discover it later, which dramatically increases the damage.
This is why advanced tools are no longer optional. For instance, businesses can implement systems for proactive fraudulent document detection to stop fake invoices before they even enter the payment pipeline. In fact, 87% of fintechs and banks agree that the cost of prevention is far less than the losses they avoid.
By pairing automated alerts from your accounting software with the access security of MFA, you create a layered technological defense that makes your business a much harder and less appealing target for fraudsters.
If you want to discuss your business law matter, contact Kons Law at (860) 920-5181.
How to Respond When Fraud Happens
Even with the best controls in place, the hard truth is that fraud can still find a way in. When it does, how you react in those first few hours is everything. Panic is the enemy; it leads to mistakes that can destroy evidence, torpedo your legal options, and turn a bad situation into a catastrophe. A swift, calm, and legally-guided response is your best tool for damage control and, hopefully, recovery.
The second you suspect fraud, your mindset has to shift from prevention to containment. This is not the time for pointing fingers or making rushed decisions. Every move you make—or don't make—will directly impact your ability to file an insurance claim, work with law enforcement, or pursue a civil case to get your money back.
Your Immediate First Steps
When you think you've uncovered fraud, the number one priority is to stop the bleeding. This means taking precise, immediate actions to lock down your systems and, just as importantly, preserve every shred of digital evidence.
- Secure Your Systems: Right away, change passwords for every account that could be affected—think email, online banking portals, and your accounting software. If you know a specific computer or device was compromised, take it off the network immediately to cut off the intruder's access.
- Do Not Delete Anything: This is a hard-and-fast rule. Make sure everyone involved knows not to delete a single email, log, or file, no matter how trivial it seems. That phishing email you want to get rid of? It's now a crucial piece of evidence. Deleting it could be seen as spoliation, or the destruction of proof.
- Avoid Tipping Off the Suspect: If you suspect the fraud is an inside job, confronting them is the worst thing you can do. It almost guarantees they will start destroying evidence. A much better approach is to discreetly revoke their system access under a believable excuse, like a planned "system update," while you quietly gather the facts.
The natural urge to "clean up" the mess is a dangerous one. Your IT team’s first instinct might be to wipe a compromised machine and start fresh, but that action erases the digital fingerprints a forensic expert needs. The rule is simple: preserve, don't purge.
Launching an Investigation Under Privilege
Once you’ve contained the immediate threat, the real investigation begins. It is absolutely critical to conduct this process under the direction of your legal counsel. This isn't just about getting good legal advice; it's about protecting the entire investigation under attorney-client privilege.
When your lawyer directs the investigation, all the communications, reports, and findings are generally shielded from being discovered by the other side in a future lawsuit. If you just have your internal team run the show, those same reports could become Exhibit A against you. Your lawyer will be the one to hire and direct forensic accountants and IT experts, ensuring they collect evidence in a way that will stand up in court and maintains that privilege.
This legal shield is becoming even more vital as regulations tighten. We're seeing a global trend toward new 'failure to prevent' fraud laws, which hold institutions directly liable for scams. This started in the UK and is spreading, signaling a major shift from "victim pays" to "business pays." The pressure on U.S. companies is mounting, highlighting the steep cost of a poorly managed fraud response. You can read more about these fraud prevention trends and their implications on Feedzai.com.
Navigating Notifications and Communications
Figuring out who to tell, what to say, and when to say it is a delicate dance. Getting it wrong—by communicating prematurely or inaccurately—can create new legal liabilities, trash your reputation, and undermine your own investigation.
Here’s the general order of operations for notifications:
- Legal Counsel: Your first call. Period. Your attorney will quarterback every other step.
- Insurance Carrier: Get your insurance provider on the phone right away. Most policies have very strict reporting deadlines, and missing one can be an easy way for them to deny your claim.
- Law Enforcement: Your lawyer will help you decide when it's the right time to bring in law enforcement, whether it's the local police or the FBI's Internet Crime Complaint Center (IC3). They'll also help you package the evidence so your report is taken seriously.
- Internal and External Communications: All messaging should be crafted with your legal team. Stick to the facts and avoid speculating. Simply telling employees that an "incident" is under investigation is usually enough—there's no need to share sensitive details.
Pursuing Legal and Financial Recovery
After the investigation uncovers what happened, your focus can finally pivot to recovery. This usually isn't a single action but a multi-pronged strategy, with your lawyer at the center of it all.
- Filing Insurance Claims: Your crime insurance or cyber liability policy is often the fastest and best route to financial recovery. The evidence you carefully preserved at the beginning will now be the foundation of your claim.
- Civil Litigation: If you can identify who is responsible—a dishonest employee, a negligent vendor, or another party—you can file a civil lawsuit to recover the stolen funds. It can be a long road, but sometimes it's the only way to be made whole.
- Demand Letters: In some situations, a strong demand letter from your attorney can be an effective first move. This is particularly true in disputes with vendors or other known parties where you want to signal you're serious before heading to court. You can learn more in our guide on how to respond to a demand letter.
A well-executed response plan can transform a potential catastrophe into a manageable crisis. If you want to discuss your business law matter, contact Kons Law at (860) 920-5181.
Building a Stronger, More Secure Business
Protecting your company from fraud isn't a one-and-done task; it’s a constant commitment. It requires vigilance, smart planning, and a deep understanding of where your vulnerabilities lie. A resilient business isn't built by accident—it’s the result of a layered defense designed to counter threats from both inside and out.
The most effective anti-fraud programs are built on a solid foundation. This starts with robust internal controls that separate key duties, making it harder for any single person to cause harm. It also means being diligent with who you hire and who you do business with, because human risk is always a factor. Finally, it involves using technology smartly to keep an eye on transactions and flag anything that looks out of place.
When you bring these elements together—strong controls, careful vetting, and smart monitoring—and back them up with a clear plan for what to do when something goes wrong, you transform your company. You shift from being a potential target to a fortified organization that takes its security seriously.
This isn't just about building defenses. It's about creating a culture of integrity that protects your bottom line, your reputation, and your future. That proactive mindset is what drives long-term stability and growth.
If you need guidance on protecting your business, whether through corporate governance, commercial litigation, or fraud recovery, we're here to help. Call Kons Law at (860) 920-5181 to discuss your situation and start building a more resilient enterprise.
Common Questions on Preventing Business Fraud
Running a business in Connecticut means you're constantly juggling priorities. It's only natural that when it comes to fraud prevention, some very practical questions pop up. Let's tackle a few of the most common ones I hear from business owners and in-house counsel.
My Business Is Small. Do I Really Need All These Fraud Controls?
Yes, absolutely. In fact, thinking you're "too small to be a target" is one of the most dangerous assumptions a business owner can make. Fraudsters specifically look for smaller companies because they bank on finding weaker controls.
The good news is that the core principles we've discussed—like segregation of duties, regular bank reconciliations, and strict vendor verification—are completely scalable. You don't need a massive accounting department to make this work. For instance, even in a two-person office, the employee who approves invoices should never be the same one who cuts the checks or initiates wire transfers. The small effort it takes to implement these basic checks and balances is nothing compared to the financial devastation a single fraud event can cause.
What's the Single Most Effective, Low-Cost Step I Can Take Today?
This one's easy: Implement a mandatory "call back" verification process for any request to change payment instructions. It's simple, powerful, and costs you nothing but a few minutes of time.
Here's the scenario: A vendor emails you, asking to update their bank account information for future payments. Your policy must require an employee to pick up the phone and verbally confirm that change. The critical part? They must use a trusted phone number you already have on file for that vendor—never a number provided in the request email itself. This one human-to-human step is incredibly effective at shutting down Business Email Compromise (BEC) and other sophisticated impersonation schemes before you lose a dime.
How Often Should We Be Reviewing Our Anti-Fraud Policies?
Think of your anti-fraud policies as a living document, not a "set it and forget it" task. At a minimum, you should be doing a comprehensive review of all your controls and procedures at least once a year.
But don't stop there. You should also trigger an immediate review anytime your business operations change significantly. That could mean bringing on a new payment processing system, hiring a new CFO or controller, expanding into a new market, or even after you successfully thwart a fraud attempt. The threat landscape is always shifting, and your defenses have to evolve right along with it.
If you need to discuss a business law matter, please call the attorneys at Kons Law at (860) 920-5181.
